Secure Mobile Data Erasure Software: A Critical Layer of Device Lifecycle Management
As mobile devices pass through trade-in, resale, and reuse programs, data security becomes a defining responsibility for businesses. Customers entrust organizations with devices that often contain highly sensitive personal or corporate information. Secure mobile data erasure software ensures that this data is permanently removed before a device continues through its lifecycle.
Within a structured Device Lifecycle Management approach, secure data erasure is not an optional step—it is a foundational requirement that protects businesses, customers, and downstream partners.
What Is Secure Mobile Data Erasure Software?
Secure mobile data erasure software is designed to permanently delete all data from a mobile device so that it cannot be recovered. Unlike basic reset functions, secure erasure follows controlled, verifiable processes aligned with recognized standards.
Key characteristics include:
- Complete removal of user and system data
- Verification that erasure was successful
- Documentation of the erasure process
- Prevention of data reconstruction
This level of assurance is essential for commercial device programs.
Why Secure Data Erasure Is a Business Necessity
Businesses managing mobile devices at scale carry significant responsibility. Data breaches resulting from improperly wiped devices can lead to regulatory penalties, legal action, and reputational damage.
Secure mobile data erasure software helps businesses:
- Meet data protection obligations
- Reduce exposure to security incidents
- Demonstrate responsible data handling
- Maintain trust with partners and customers
Without secure erasure, even well-managed device programs remain vulnerable.
Supporting Customer Confidence Through Responsible Practices
Although secure data erasure software operates behind the scenes, its impact is felt by customers of the business.
When businesses implement reliable erasure processes, customers benefit from:
- Assurance that personal data is protected
- Confidence in trade-in and return programs
- Trust in device reuse and resale practices
This confidence is essential for sustaining customer participation in device programs.
Secure Data Erasure Within Device Lifecycle Management
Secure mobile data erasure software is most effective when integrated into a complete Device Lifecycle Management workflow.
Within lifecycle processes, erasure typically follows:
- Device intake and eligibility checks
- Functional diagnostics
- Preparation for reuse, resale, or recycling
This structured sequencing ensures that data is erased at the correct stage and under controlled conditions.
Bulk Data Wiping for High-Volume Operations
Businesses processing large volumes of devices require efficiency without compromising security. Device Lifecycle Management software supports bulk data wiping, allowing multiple devices to be erased simultaneously.
It is important to note:
- Parallel processing applies only to data wiping
- Other lifecycle steps are handled individually
- Each device’s erasure is tracked separately
This approach balances speed with accountability and compliance.
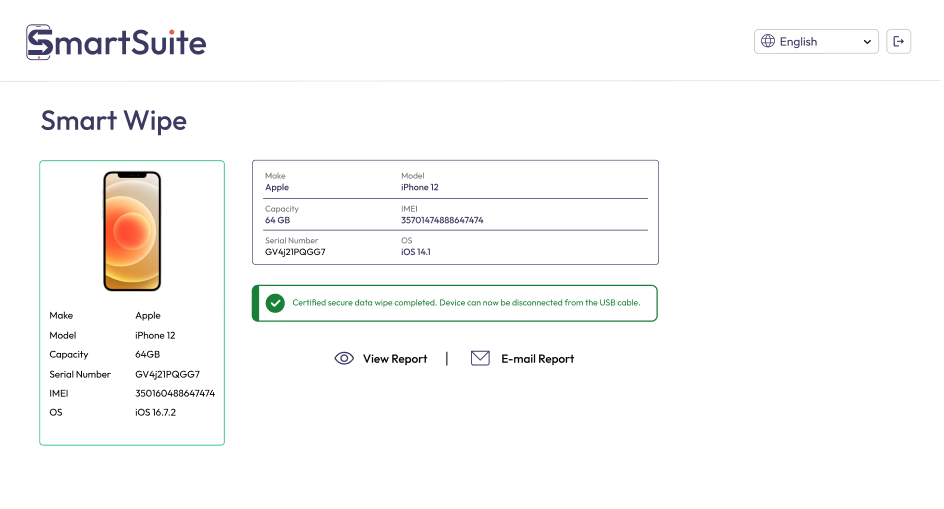
Verification and Proof of Erasure
Secure mobile data erasure software does more than delete data—it verifies that the process was completed successfully.
Verification enables:
- Confirmation that no data remains
- Detection of erasure failures
- Generation of audit-ready records
These records are critical for demonstrating compliance and supporting downstream activities such as resale.
See also: The Biggest Gaming Tech Disruptions Coming in 2026: What to Watch and Why
Compliance and Regulatory Alignment
Data protection regulations increasingly require businesses to prove that data has been securely destroyed. Secure erasure software supports compliance by producing clear, traceable documentation.
Businesses gain:
- Evidence for audits and inspections
- Reduced regulatory risk
- Improved contractual compliance
This documentation strengthens governance across device programs.
Protecting Secondary Market Integrity
Devices entering secondary markets must be free of data to protect new users and partners. Secure erasure ensures that devices are safe for resale or redeployment.
Benefits include:
- Reduced risk for buyers and partners
- Stronger resale relationships
- Increased market confidence
Secure data erasure is a prerequisite for responsible recommerce.
Centralized Oversight and Reporting
Lifecycle-focused software centralizes erasure activity, giving businesses clear visibility into data security performance.
Centralized oversight allows:
- Tracking of erasure status across devices
- Consolidated reporting
- Faster issue resolution
This visibility supports operational control and continuous improvement.
Scaling Secure Practices with Growth
As device programs expand, secure data erasure must scale seamlessly. Automated erasure processes ensure consistency regardless of volume or location.
Scalable advantages include:
- Uniform security standards
- Reduced reliance on manual processes
- Faster processing times
This scalability enables sustainable growth without increasing risk.
Conclusion
Secure mobile data erasure software is a critical pillar of Device Lifecycle Management. By ensuring permanent, verifiable data deletion, businesses can protect customer information, meet regulatory requirements, and maintain trust across the device ecosystem.
When integrated into lifecycle-focused workflows—and supported by bulk data wiping for efficiency—secure data erasure software enables businesses to operate compliant, secure, and scalable device programs in an increasingly data-sensitive world.




